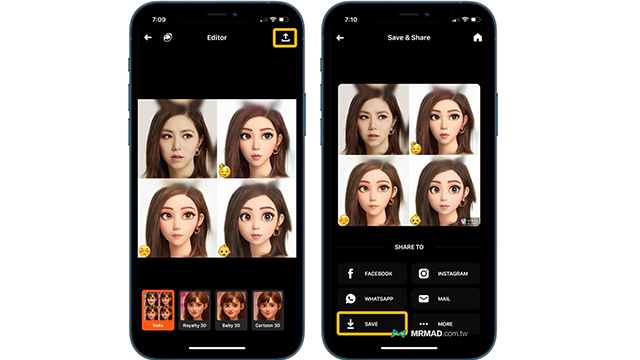
Check Point Research (CPR) conducts a preliminary security analysis on Voila app, the popular app that turns a person into a cartoon avatar. Although there are no obvious red flags at this time, CPR highlights the potential risk in the fact that Voila app sends face pictures to its servers for processing. Face pictures, along with user identification details, could end up in malicious hands, in the event of a cyber attack.
- Voila app sends face photos to its servers for processing
- The app includes specific and unique installation ID (vdid) generated by Google Play when it sends photos for verification
- Face photos are linked to specific user installation details. Where in the event of a cyber attack, face photos and user details can potentially end up in malicious hands
Check Point Research (CPR) has ran a preliminary security scan on Viola app, the increasingly popular app that turns a person into a cartoon avatar. Below are CPR’s initial notes at this time:
- The app has been written by a legitimate LLP company registeredin the United Kingdom (UK)
- In terms of permissions, the app utilizes only the bare minimum required for operation.
- The app verifies that the images contain face(s), and only after that verification, the app sends them to the server for processing
- All communication with the server are performed using HTTPS, so the traffic is encrypted out-of-the-box
- The app is using well known open source libraries, where possible
- When the photo is sent to the server, the app includes the specific and unique installation id (vdid) that was generated by Google Play, potentially linking faces to the specific installation
Yaniv Balmas, Head of Cyber Research at Check Point Software “Most users likely assume that the processing of Voila app is done locally on their phone. This is not the case. A non-obvious fact here is that the company sends face pictures to its servers for processing. When a face photo is sent to the company’s server, the app includes unique installation IDs that were generated by Google Play. So each photo is packaged up with user identification details. While this fact is mentioned in the company’s privacy policy, the possibility for misuse of the data opens up – either by the company itself or by a 3rd party. For example, if the company is hacked, the attackers could potentially gather a large data base of all faces of application users. We have no way of telling if the company is doing anything illegal or malicious, but I do think it’s important for new users to be aware of the inherent risks in sending content to servers for processing. The risk being pictures of your or your loved ones face in malicious hands, in the event of a data breach or cyber attack.”